The digital landscape, a realm of unparalleled innovation and opportunity, is simultaneously a hotbed of evolving threats. As organizations increasingly rely on interconnected systems and cloud infrastructure, safeguarding these vital assets becomes paramount. Navigating this intricate environment requires a robust defense strategy, and at its core lies the effective implementation of technical controls in cyber security. In this article, DoctinOnline will accompany you to explore the critical role these controls play, demystifying the jargon and offering a clear understanding of how they function to protect your digital world, and the forward-thinking strategies required to build true digital resilience.
Understanding Technical Controls in Cyber Security
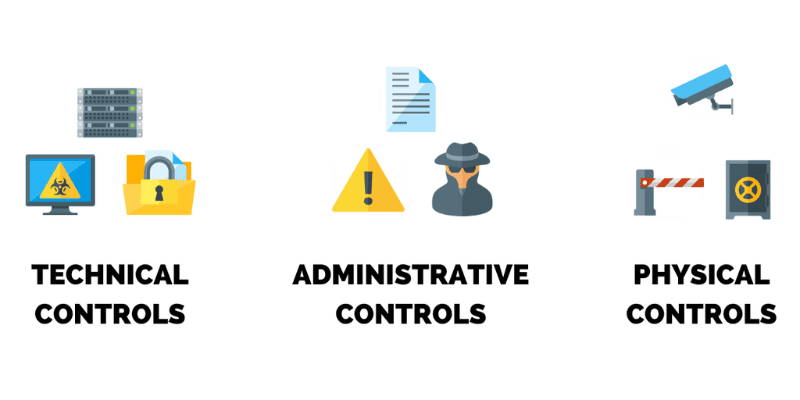
At the foundational layer of any comprehensive cybersecurity framework are technical controls in cyber security. These are the safeguards embedded within information systems, hardware, and software that enforce policies and procedures to protect the confidentiality, integrity, and availability of data. Unlike administrative controls, which focus on human behavior and policies, or physical controls, which secure the environment, technical controls operate directly on the technology itself, acting as digital gatekeepers and watchful sentinels. They are engineered to detect, prevent, and respond to threats automatically or semi-automatically, forming the bedrock of a secure operational posture. Without these vital automated and programmatic defenses, even the most well-intentioned policies and robust physical security measures can be easily bypassed by determined attackers.
The importance of well-architected technical controls cannot be overstated in today’s threat landscape, where attack vectors are constantly shifting and becoming more complex. Recent reports indicate a significant rise in cyberattacks, with businesses facing substantial financial losses and reputational damage. Investing in and continually refining these controls is not merely a compliance checkbox but a strategic imperative for long-term business continuity and trust.
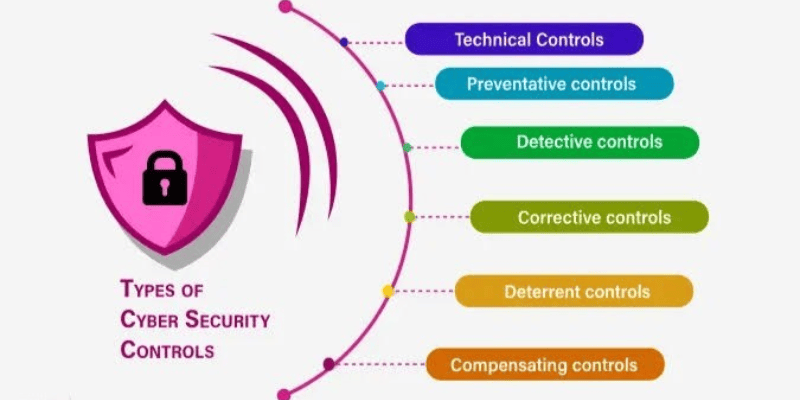
Categories of Technical Controls and Their Application
Technical controls in cyber security are typically categorized based on their primary function in the defense lifecycle: preventative, detective, and corrective. Each category plays a distinct yet interconnected role, working in concert to form a multi-layered defense strategy. A holistic approach demands the integration of all three types, creating a resilient architecture that not only stops attacks but also identifies breaches quickly and remediates their impact efficiently. Understanding these classifications is crucial for designing a security infrastructure that can anticipate, identify, and recover.
Preventative controls
Preventative controls are designed to stop security incidents.
Examples of preventative controls include:
- Firewalls: These network security devices monitor and filter incoming and outgoing network traffic based on predefined security rules. They create a barrier between a trusted internal network and untrusted external networks, preventing unauthorized access. Modern firewalls often incorporate advanced threat intelligence and application-layer inspection to block sophisticated attacks.
- Access Control Lists (ACLs): ACLs specify which users or system processes are granted access to objects or resources, as well as what operations are allowed on given objects. They are fundamental in enforcing the principle of least privilege, ensuring that users only have the permissions necessary to perform their legitimate tasks. This granular control minimizes the risk of privilege escalation and unauthorized data access.
- Encryption: This process transforms information into a code to prevent unauthorized access. Data encryption protects sensitive information both at rest (e.g., on hard drives) and in transit (e.g., over networks), making it unreadable to anyone without the correct decryption key. Strong encryption is vital for safeguarding confidential data against interception and theft, especially in cloud environments.
- Patch Management: Regularly applying security patches and updates to operating systems, applications, and firmware closes known vulnerabilities that attackers could exploit. A consistent and timely patch management program is critical for maintaining system integrity and preventing exploits.
Detective controls
Detective controls are deployed to identify and alert security personnel to security incidents that have already occurred or are currently underway. Their primary goal is to minimize the window of opportunity for attackers by providing timely visibility into malicious activities. Rapid detection is crucial for mitigating the damage of a breach and initiating an effective response before significant harm is done. These controls act as the vigilant eyes and ears of the security team, continuously monitoring systems for anomalous behavior or indicators of compromise.
Key detective controls include:
- Intrusion Detection Systems (IDS): IDSs monitor network traffic or system activities for malicious activity or policy violations and generate alerts when suspicious events are detected. They can be network-based (NIDS) or host-based (HIDS), providing comprehensive coverage. Advanced IDSs use behavioral analysis to spot deviations, identifying zero-day threats.
- Security Information and Event Management (SIEM) Systems: SIEM solutions centralize and analyze security logs and event data from various sources across an organization’s IT infrastructure. They correlate events, identify patterns, and provide real-time alerts and dashboards for security analysts, offering a holistic view of the security posture. SIEMs are indispensable for incident response and compliance reporting.
- Vulnerability Scanners: These tools automatically identify security weaknesses in applications, networks, and systems. Regular scanning helps organizations proactively discover and address vulnerabilities before attackers can exploit them. While preventative in their outcome, the act of scanning itself is a detective measure to find existing flaws.
- Security Audits and Logging: Comprehensive logging of system events, user activities, and network traffic provides a crucial forensic trail for investigating incidents. Regular security audits, often performed by external parties, assess the effectiveness of existing controls and identify gaps or non-compliance issues. Proper logging is a non-negotiable component of any robust security strategy.
Corrective controls
Corrective controls are put in place to restore systems and data to a secure state after a security incident has occurred. They focus on minimizing the damage, containing the breach, and facilitating recovery operations. The effectiveness of corrective controls directly impacts an organization’s ability to bounce back.
Examples include:
- Incident Response Plans: Detailed, well-practiced plans outline the procedures and responsibilities for handling security incidents, and post-incident analysis. A clear incident response plan is paramount for a swift and organized reaction to a breach, minimizing its impact.
- Data Backups and Recovery Systems: Regular and secure backups of critical data, coupled with robust recovery mechanisms, ensure that information can be restored quickly and accurately after data loss or corruption due to an attack. Offsite and immutable backups are crucial for protecting against ransomware and other destructive attacks.
- Anti-malware and Antivirus Software: These tools are not only preventative but also corrective, as they can detect and remove malicious software, disinfect infected systems, and restore them to a clean state after an infection. Their ability to neutralize active threats makes them a vital component of any corrective strategy.
- Disaster Recovery Planning (DRP): DRP focuses on an organization’s ability to resume normal operations after a major disruption, including cyberattacks. This involves having redundant systems, alternative sites, and tested procedures for restoring critical business functions and data quickly. A well-defined DRP ensures business continuity even in the face of significant security events.
Architectural Considerations for Technical Controls
Designing an effective architecture for technical controls in cyber security requires strategic thinking, considering the evolving threat landscape and the unique needs of an organization. It’s not merely about deploying individual tools but integrating them into a cohesive and layered defense system. Modern cybersecurity architectures prioritize concepts like “Zero Trust” and “Defense in Depth” to create a more resilient and adaptable security posture. The goal is to build a framework where security is not an afterthought but an intrinsic part of every system and process, adapting to dynamic threats and an increasingly distributed IT environment.
Zero Trust architecture
The Zero Trust security model operates on the principle of “never trust, always verify.” This means that no user, device, or application is inherently trusted, regardless of whether it is inside or outside the network perimeter. Every access request is rigorously authenticated, authorized, and continuously validated before access is granted. This paradigm shift from traditional perimeter-based security is becoming essential as organizational boundaries blur with remote work and cloud adoption. Implementing Zero Trust requires robust identity and access management (IAM), micro-segmentation, and continuous monitoring, transforming how organizations deploy their technical controls in cyber security.
Defense in depth
Defense in Depth is a security strategy that employs multiple layers of security controls to protect information. If one control fails, another is there to provide protection. This multi-layered approach makes it significantly harder for attackers to penetrate an organization’s defenses, as they must bypass several independent security mechanisms. This strategy applies across all control types: physical, administrative, and technical. For instance, a firewall (preventative) might stop an initial intrusion, but an IDS (detective) would catch any attempt to move laterally within the network if the firewall were somehow bypassed. Each layer strengthens the overall security posture, reducing the risk of a single point of failure leading to a catastrophic breach.
The Evolution of Technical Controls with AI and Automation
The rapid advancements in artificial intelligence (AI) and automation are profoundly transforming the landscape of technical controls in cyber security. As cyber threats become more sophisticated and numerous, relying solely on human intervention for monitoring and response is unsustainable. AI and automation offer the promise of intelligent, proactive, and scalable security solutions that can analyze vast amounts of data, identify anomalies with greater accuracy, and respond to threats at machine speed. This integration is not just an enhancement but a fundamental shift in how organizations can effectively defend their digital assets against an increasingly automated adversary.
AI-powered security tools can perform complex tasks that were once exclusively the domain of human analysts. Machine learning algorithms, for instance, are exceptionally good at identifying patterns in network traffic or user behavior that indicate malicious activity, often detecting threats that would evade traditional signature-based systems. This includes recognizing novel malware variants, insider threats, and sophisticated phishing campaigns. Automated response mechanisms, triggered by AI insights, can then take immediate action, such as isolating an infected host, blocking malicious IP addresses, or revoking user access, thereby significantly reducing response times and mitigating potential damage.
The deployment of AI and automation within technical controls extends to various critical areas:
- Threat Intelligence and Prediction: AI can analyze global threat intelligence feeds, identify emerging attack trends, and even predict potential future vulnerabilities, allowing organizations to proactively strengthen their defenses.
- Security Orchestration, Automation, and Response (SOAR): SOAR platforms leverage AI and automation to streamline security operations. They automate routine tasks, orchestrate complex workflows between different security tools, and guide analysts through incident response procedures, improving efficiency and consistency.
- Behavioral Analytics: AI-driven User and Entity Behavior Analytics (UEBA) systems learn normal behavior patterns for users, devices, and applications. They then flag any deviations, or advanced persistent threats (APTs).
Vulnerability Management: AI can enhance vulnerability scanning by prioritizing vulnerabilities based on real-world exploitability and potential impact, helping security teams focus their efforts on the most critical risks.
- As Satya Nadella, CEO of Microsoft, has emphasized, “Cybersecurity is the number one challenge of the digital age.” The integration of AI and automation into technical controls in cyber security is crucial for meeting this challenge, providing the scale and intelligence needed to protect against ever-evolving threats.
Measuring and Optimizing Technical Control Effectiveness
Implementing technical controls in cyber security is only the first step; their true value lies in their ongoing effectiveness. Organizations must continuously measure, evaluate, and optimize these controls to ensure they remain robust against a dynamic threat landscape. This requires a proactive approach, utilizing metrics, regular testing, and continuous feedback loops to adapt and improve security posture. A static set of controls will quickly become obsolete, emphasizing the need for an agile and iterative security management process.
Key aspects of measuring and optimizing effectiveness include:
- Security Metrics and KPIs: Defining clear security metrics and Key Performance Indicators (KPIs) is essential for tracking the performance of technical controls. Examples include mean time to detect (MTTD), mean time to respond (MTTR), number of successful blocks by a firewall, patch compliance rates, or the number of critical vulnerabilities remediated. These metrics provide tangible insights into control efficacy.
- Regular Testing and Audits:
- Penetration Testing: Ethical hackers simulate real-world attacks to identify exploitable vulnerabilities and evaluate the effectiveness of preventative and detective controls.
- Vulnerability Assessments: Automated tools scan systems and applications for known weaknesses.
- Red Team / Blue Team Exercises: Red teams act as adversaries, attempting to breach defenses, while blue teams defend and respond, providing valuable training and identifying gaps in technical controls.
- Continuous Monitoring and Feedback: Modern security operations centers (SOCs) leverage continuous monitoring tools like SIEMs and SOAR platforms to gather real-time data on control performance. This constant flow of information allows for immediate adjustments and fine-tuning of controls based on observed threats and system behavior.
- Threat Modeling: Regularly performing threat modeling helps organizations anticipate potential attack vectors and adapt their technical controls accordingly. By understanding hypothetical attacks, security teams can proactively strengthen defenses.
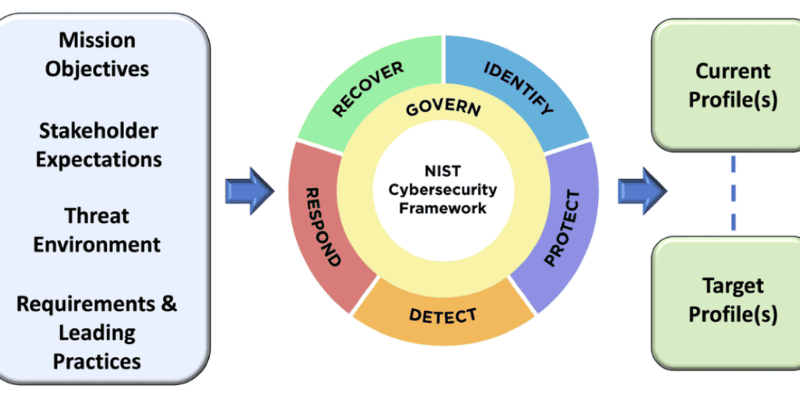
- Compliance and Regulatory Requirements: Adhering to industry standards (e.g., ISO 27001, NIST Cybersecurity Framework) and regulatory mandates (e.g., GDPR, HIPAA) often necessitates specific technical controls and provides a baseline for effective security. Regular audits against these frameworks help validate control effectiveness.
Conclusion
The journey through the intricate world of technical controls in cyber security reveals their indisputable role as the bedrock of digital defense. From firewalls to AI-driven behavioral analytics, these sophisticated mechanisms are the guardians of our interconnected existence, working tirelessly to protect data, systems, and reputations. As threats evolve, so too must our approach to these controls, embracing adaptive architectures like Zero Trust and leveraging the power of AI and automation for proactive defense. DoctinOnline encourages you to view these controls not as mere tools, but as critical investments in resilience and operational continuity. By continuously evaluating, optimizing, and staying ahead of the curve, you can ensure your digital assets are fortified against the challenges of tomorrow. To further enhance your cybersecurity posture and make informed decisions, explore DoctinOnline’s extensive library of articles on emerging cyber threats and cutting-edge security solutions.

